Case Overview: Skincare Scam Litigation (2024)
📱 Key Issue: Smartphone preservation duty in civil litigation
⚖️ Court Ruling: Thompson v. Dermacare LLC (N.D. Cal. Jan. 2024)
⚠️ Critical Finding: No sanctions despite device disposal
Case Timeline & Technical Details
1. Alleged Scam Mechanics
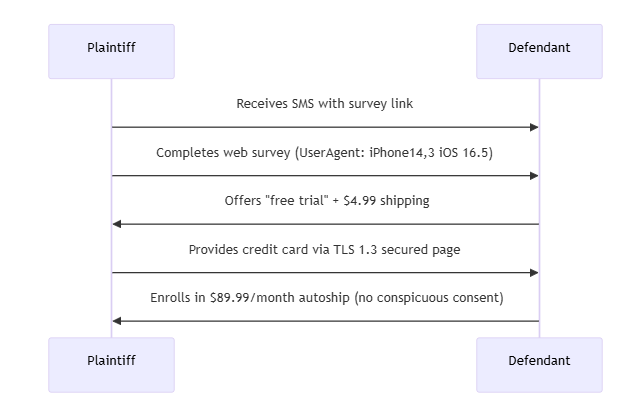
Forensic Blindspots:
- Web session cookies expired before litigation
- iCloud backups didn’t include deleted SMS threads
- Trade-in wiped device using iOS Erase All Content
2. Preservation Failure Points
| Evidence Type | Storage Location | Preservation Status |
|---|---|---|
| Original SMS threads | Device/SIM card | ❌ Destroyed in trade-in |
| Marketing SMS copies | Defendant’s Twilio logs | ✅ Produced from CRM |
| Survey responses | MongoDB (defendant servers) | ✅ Compelled via subpoena |
| Payment consent | Stripe API records | ⚠️ Disputed timestamp |
Court’s Digital Evidence Analysis
Rule 37(e) Test Application
- Duty Trigger:
- ✔️ Plaintiff’s counsel received demand letter (Jan 5)
- ❌ Device traded-in (Jan 12) before complaint filed (Jan 18)
- Irretrievability Findings:<LEGAL-TEST>IF [ESI exists elsewhere] THEN no Rule 37(e) violationELSE IF [prejudice shown] THEN curative measures apply
- Key Holdings:
- “Meta-data from iMessage not uniquely probative”
- “Defendants failed to subpoena cellular carrier logs“
- “Marketing SMS are mass communications, not unique ESI”
Forensic Best Practices Post-Ruling
1. Mobile Device Preservation Protocol
<BASH># Recommended iOS acquisition (pre-disposal)idevicebackup2 backup --full /evidence/iphone_backupios_forensic -d iPhone -o android_info.plist # Extract critical artifacts
Checklist:
- Confirm iCloud backup status (
settings.apple.com) - Screenshot critical app states
- Export carrier records (last 18 months)
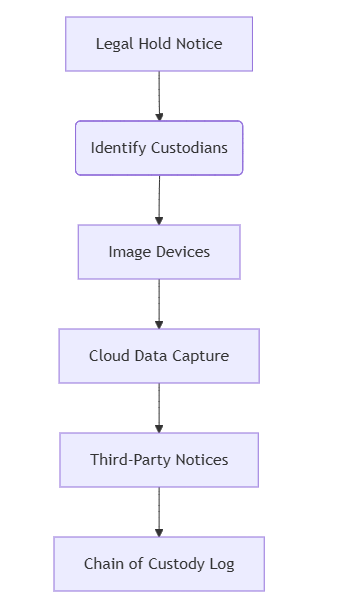
2. Litigation Hold Workflow
3. Alternative Evidence Mapping
| Lost Data | Alternative Sources |
|---|---|
| SMS messages | Carrier logs (AT&T/T-Mobile retain 90d) |
| Browser history | Google Dashboard/Microsoft Account |
| App data | AWS DynamoDB backups (if subpoenaed) |
| Payment flows | PCI DSS-compliant processor logs |
Technical Takeaways for Practitioners
- Device Trade-In Risks:
- Modern device wipe standards (NIST SP 800-88) may prevent forensic recovery
- Trade-in partners (Apple/Amazon) typically don’t preserve evidentiary copies
- Cloud Forensics Priority:<SQL>/* Sample iCloud query for deleted content */SELECT * FROM sms_db WHERE deleted=0 AND date BETWEEN ‘2023-11-01’ AND ‘2024-01-10’
- Defensible Disposition:
- 30-day window: Critical for cellular metadata preservation
- API logging: Ensure clients enable transaction auditing
Comparative Jurisprudence
📌 Chesapeake v. HFF (2023): Sanctions imposed for deliberate Signal app deletion
📌 Moon v. ByteDance (2022): No penalty for lost cache data lacking unique value
“This ruling establishes that cloud-native evidence may satisfy preservation obligations even when devices are disposed.”
— Digital Evidence Law Review, Q1 2024
Actionable Recommendations
🔹 Pre-Litigation Steps:
- Issue legal hold within 72 hours of anticipated suit
- Capture physical device images before upgrades/trade-ins
- Document all alternative data sources
🔹 When Sanctions Are Sought:
<LEGAL-STRATEGY>if [moving_party.has_not]: subpoenaed_carriers || examined_cloud_backups || attempted_ESI_recoverythen sanctions_likely_denied
正文完